Security is sometimes compared to healthy food. Quite a nice analogy: we all know we should eat healthy but we don’t always do it. The same is true for security: even though we know security measures are important, we sometimes favour a situation that is less secure. For various reasons.
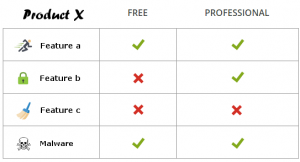
Last September a lot of users got infected with malware when they downloaded the CCleaner update. Hackers had been able to hide the Floxif Trojan inside the installer of the update. CCleaner is a utility program used to clean potentially unwanted files and invalid Windows Registry entries from a computer. This is a chart from…
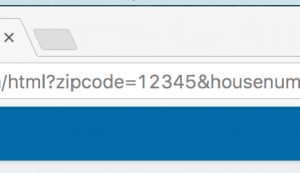
Parameters in the url (GET parameters) are used to pass information to the destination on the target server. Quite often I see cases where these GET parameters are used to transmit personal data. For example, a company sends out a newsletter to their clients with a link to their website where they want to personalize…
- « Previous
- 1
- 2
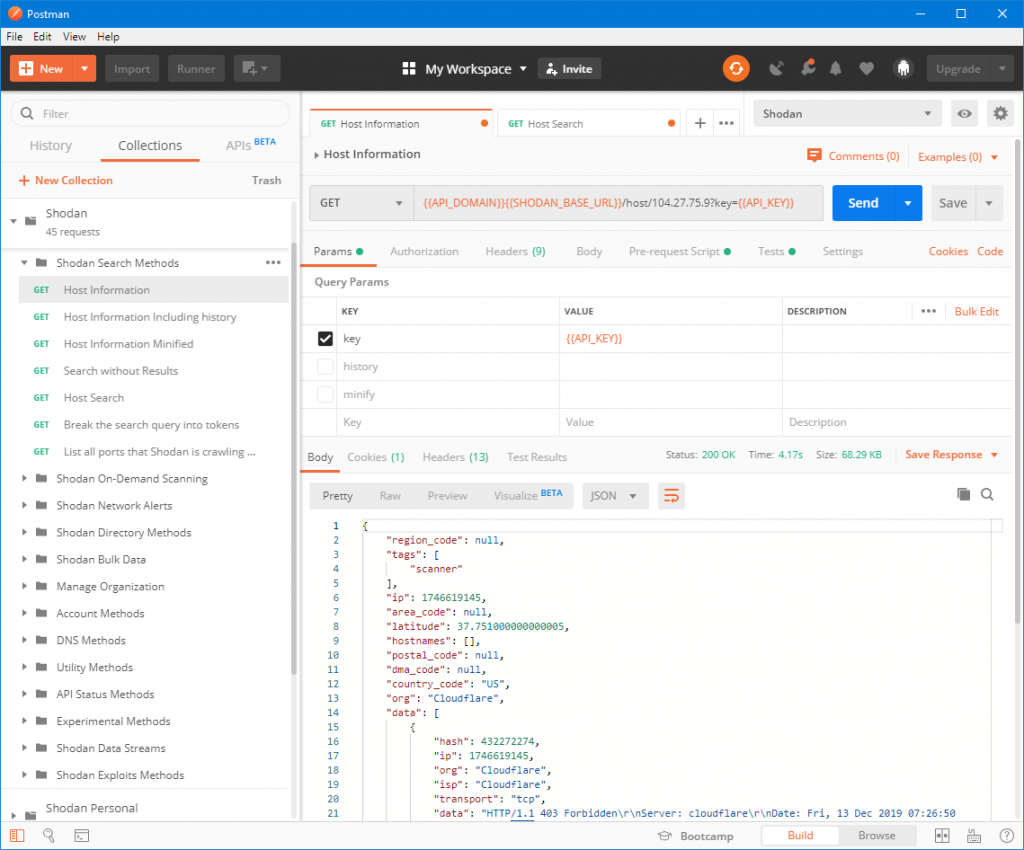
Shodan Postman Collection
The Christmas holidays are coming and to those of you who feel like doing something adventurous: there is now a new way to visit the dark caverns of the internet. We created an exciting combination of two existing services that make this trip possible: A Postman collection of all the currently available Shodan API calls….
Mitigating CVE-2019-11358 in old versions of jQuery
A few months ago, a new vulnerability was found in jQuery, affecting all existing versions of jQuery. It was fixed only in the new version 3.4.0.The SNYK website has a lot of detailed information about this ‘Prototype Pollution’ vulnerability, so I won’t go into that here. For those interested, follow this link : https://snyk.io/vuln/SNYK-JS-JQUERY-174006 What…
Two Factor Authentication Cross Site Request Forgery (CSRF) vulnerability (CVE-2018-20231)
At BitnessWise we recently did a review of a few Two Factor Authentication (2FA) plugins for WordPress. First we selected some candidates based on usability and free-version features and after that performed a technical review of the plugin. This revealed a vulnerability we’d like to discuss in this post for future reference and to better…
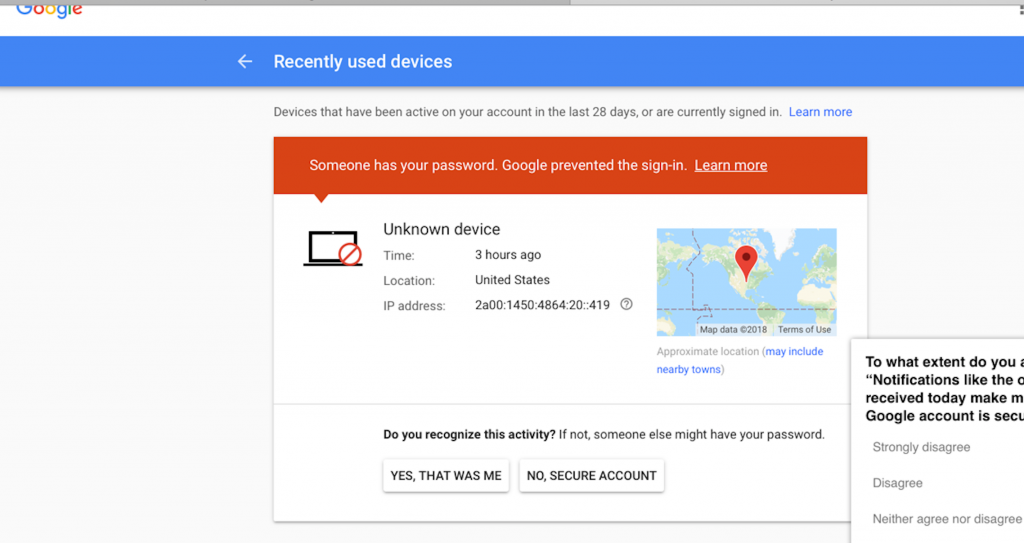
We prevented a sign-in attempt
Last weekend, almost exactly between April Fools’ Day and Halloween, Google played a prank and scared us! If you have used Gmail on different devices, you probably know the kind of message you get when you log in from a different device. Additionally, you might be presented with a security question if Google doesn’t trust…
Don’t trust Google Links
Phishing campaigns are lucrative and probably will continue to be so for a while longer: they are cheap to launch and it only takes a few recipients that click on your malicious link to be successful. But awareness about the dangers of clicking on links is slowly rising. So if you’re a bad guy, how…



 .
.